The recent breach information on AIO-TLP370 with regards to TheJavaSea.me has sent grave alerts to the cyberspace, enterprise IT and digital governance industries. This breach signifies something more than just any other data leakage, it reflects significant weaknesses in storage, transfer and security of critical tools, enterprise systems and operational data. Enterprise reliance over automation, log processing tools and integrated solutions is rapidly growing and a breach of this magnitude reveals profound security shortcomings.
Table of Contents
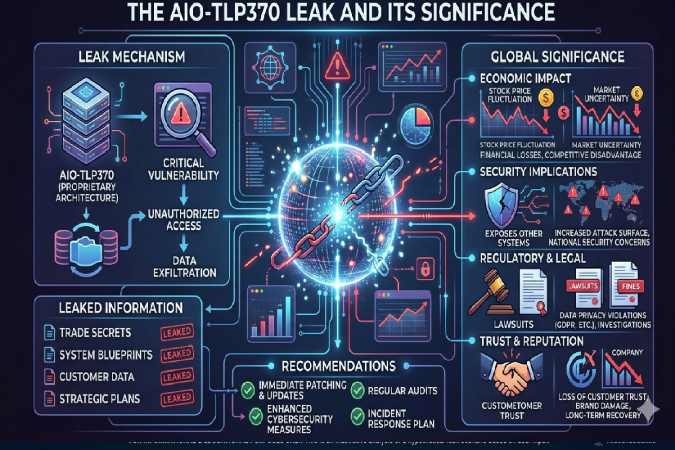
The AIO-TLP370 Leak and its Significance
The AIO-TLP370 leak discovered on TheJavaSea.me has been described as containing a large database. Which is comprised of internally generated system data, source code, configurations, operating information, and credentials. This data is not simply the data of an organization. It goes beyond information describing what it has done in the external world and is the description, the blueprint, of the organization’s internal workings-its logical architectures, processes of authorization, and design choices.
The data which this type of leak is inherently capable of exposes highly valuable information because. By showing how an organization’s internal tools are structured and operate-the organization’s log processors and automation applications. For example-attackers will not only have a glimpse at its defenses and threat analysis but will be given a direct path to navigate past them and hide their activities.
The consequence of the significance of leaks such as this-or what we might term, the importance of the matter is-the current consequence of these security failings which are not simply technical problems anymore but strategic issues that affect an entire business.
Main security risks caused by the breach
There are several threats from AIO-TLP370 compromise that go far beyond the reach of the actual data disclosed: credential disclosure is one of the biggest risks, if api keys, access tokens or secrets are included in the leak. This gives the attacker direct, and sometimes indirect, access to operational systems. Even if the credential has already been revoked the attacker may be able to derive other, and possibly more critical secrets from it.
Source code disclosure presents another very important threat. A proprietary code can be studied line by line, searching for errors and logic flaws in the code, and even in unpatched software components of a system. This would hugely increase the attacker’s work of achieving privilege escalation, data exfiltration or data manipulation.
Details about internal processes and operations may be discovered during operational intelligence disclosure. An attacker could use these details to plan the attack so as to be able to overwhelm systems or that there would be little probability of its discovery.
Primary Security Concerns Identified:
- Unauthorized access to confidential login credentials, API keys, etc.
- Increased risk of automated, complex attacks
- Re-engineering of internal mechanisms, tools
- Common vulnerabilities in the leaked code exploited
- Compromised security incident response, monitoring mechanisms
- Increased supply chain and lateral movement threats
Effect on Organisations and their Environment
The breach of TheJavaSea.me AIO-TLP370 is not only relevant to its source. Any organization that uses, is connected to, or relies upon any of the systems that are compromised by this leak is a victim, even if they were not the direct target. This is because they may share libraries, use common credentials or system configurations, which could similarly present a threat.
In a business setting the impact can be overwhelming. Among the myriad effects of data breaches is potential for operational disruption, financial loss, legal repercussions, and a complete lack of confidence and trust from customers, business partners, and other stakeholders, all of whom trust the organizations with whom they do business to secure their data. Loss of trust could take considerable time and cost a significant sum to regain.
The reputation of the compromised organization could take a substantial hit. In today’s environment, purchasing decisions and business partnerships could be significantly influenced by the security incident, and investors may also cease to trust the business. An organization within the breached company’s ecosystem will be under closer scrutiny, even if not named on the leak.
Legal, Compliance and Governance Implications
All nearly all countries have laws mandating that businesses protect private information and confidential data from unauthorized disclosure. In cases such as a leak of internal systems configurations and operating data, the organization can be held accountable for not having secure systems, poor access controls and inadequate security policies. The legal framework requires them to demonstrate compliance with the relevant business security standards.
Depending on the circumstances, mandatory breach notifications may be required of the organization. Organizations can also face significant fines, both internationally and through certain regulatory agencies. The AIO-TLP370 event also serves as a stark reminder of the importance of good corporate governance for cybersecurity, which should be at the forefront of decision making and not delegated to IT technicians.
AIO-TLP370 breach and key lessons learned:
Perhaps the most prominent lesson to take away from this breach is the threat imposed by centralized access of highly sensitive assets with limited supervision. This attack illustrates that there is no longer viability in hiding an system, and rather an organization must prepare for the inevitable compromise of internal systems by designing around it.
Another key takeaway is the importance of ongoing vigilance and the handling of credentials. Embedded static secrets and outdated and static controls present enormous security risks that can ultimately compromise the entire network and further than that. In order to be properly protected it must be recognized that it is best to have a reactive posture rather than a proactive posture, where audits, automated threat detection, and quick credential replacement/revocation are implemented.
Finally, this breach highlights the importance of supply chain security. No matter how robust internal security systems may be, a vulnerable third-party application could pose an enormous threat.
Remediating Best Practices:
- Immediately revoking/rotating all credentials that were exposed
- Conducting in-depth checks of all source code and system configurations
- Implementing zero-trust principles within system architecture
- Monitoring of the system in order to observe system activity after the breach and look for anomaly indicators
- Enhancing diligence of third-party suppliers and the supply chain controls used
- Developing sound security incident response and notification procedures
Long-term security strategic implications:
The compromise of AIO-TLP370 illustrates an expectation that the security community has already forecast: that attackers are moving past user accounts to attack development tools, internal operating systems, and internal systems themselves, and thereby gain an unprecedented level of leverage and access to internals.
Security teams will need to change: Perimeter defenses are no longer sufficient; internal systems (tools, operating systems, automation, and administrative platforms) will need to be secured as strenuously as customer-facing systems. This transition from edge defenses will require the establishment of:
- Threat modeling internal infrastructure.
- Continuous validation of internal assets.
- Disaster preparedness. The price to avoid such a compromise is infinitesimal when compared to its remediation.
Conclusion:
The TheJavaSea.me Leak AIO-TLP370 is not a isolated incident, but a warning. This leak shows how tightly integrated systems are today. And how quickly an exploit can spread throughout organizations and across industries. The security implications and impact of this leak make it clear. How essential it is to reinforce governance, improve security proactively, and foster a culture of accountability.
If organizations learn from this incident and implement strong. Flexible security measures they will be better able to survive future threats. But the organizations that do not heed these warnings risk suffering the same fate over and over again, at a much higher price.
FAQs
- What is thejavasea.me leaks aio-tlp370?
Thejavasea.me leaks aio-tlp370 refers to the internet technology community news. About the rumored data leak of digital files associated with thejavasea.me website.
- Can you download thejavasea.me leaks aio-tLP370?
Users should refrain from downloading anything associated with thejavasea.me leaks aio-tlp370, as it may contain malicious and illegal data.
- Why are people searching for thejavasea.me leaks aio-tlp370?
People search thejavasea.me leaks aio-tlp370 in an effort to obtain information. On what data the file contained and if sensitive content is present within.
- What actions can users take to protect themselves from leaks like thejavasea.me aio-tlp370 leaks?
Users can protect themselves from a similar leak event by using secure passwords. Enabling two-factor authentication, refraining from downloading unsuspicious applications, and consistently updating their software.
- Where can I obtain more information about technology concerns and thejavasea.me leaks aio-tlp370?
Data security information, along with that pertaining to topics like thejavasea.me leaks aio-tlp370. It can be found through numerous technology blogs, cybersecurity tutorials, and online resources.
